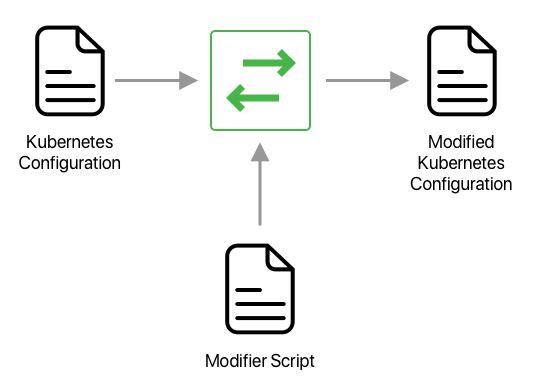
Deploying applications onto Kubernetes is done mostly through configuration files. Each service within your application is deployed to a Kubernetes cluster through a set of configuration files that define how infrastructure resources should be described and managed. These configuration files are usually defined by developers who develop the application. However to monitor and maintain the cluster, operators (Ops) sometimes need to add their own resources to the mix, to make sure the cluster is monitored, managed and maintained for everyone.
This sometimes means augmenting developer crafted configuration files to add new components to it: for example, operators might need to make sure all traffic to and from the services are encrypted or they might want to send all application logs into a central log facility.
Enforcing those policies and best practices can be challenging. Earlier this year, we released Copper, an open source configuration validator for Kubernetes. Copper can read and enforce user-defined rules before a configuration file is applied to a cluster. It however cannot make changes to the configuration files themselves.
Today, we are excited to release Alterant, another Cloud 66 open source product which does exactly that: it changes configuration files based on your instructions.
The concept of altering configuration files before they are applied to the cluster is not new. Kubernetes Admission Operators have been around for a while and can be used to modify resources upon addition. Alterant however, aims to make these changes simpler, and more importantly, transparent. Alterant doesn't talk to your Kubernetes cluster, but it generates the modified configuration files based on your scripts so you can put them in your own deployment automation pipeline.
Alterant support is coming soon to Cloud 66 Skycap, allowing Skycap users to apply their Alterant modifier scripts during the deployment workflow in Skycap.
We hope you enjoy using Alterant! Let us know what you think and feel free to share the love!