Firewalls are too important to get wrong. They can also be complicated to set up and more complicated to maintain. Before using Cloud 66, I would find myself asking this question quite a lot: "Should this port be open?" Many of those mystery ports are left open because no one is sure which service is using them and what happens if we now close them.
I think this is because of two main reasons: First, firewalls are just lists of numbers. They don't have an audit log (who opened this port, when and why) or any descriptions next to them.
The other reason is that they are separate from the application. As your applications evolve, so do your firewall requirements, but most of the time firewalls end up being an accumulative list of all ports your application has ever used.
How does it work?
This is why when we started Cloud 66, we knew we wanted to change this by adding audit logs, descriptions, tags to each firewall rule. But even more importantly, Cloud 66 firewalls are application-driven: this means they react to the application's needs and open and close ports based on that.
Here is an example of what a Cloud 66 firewall looks like:
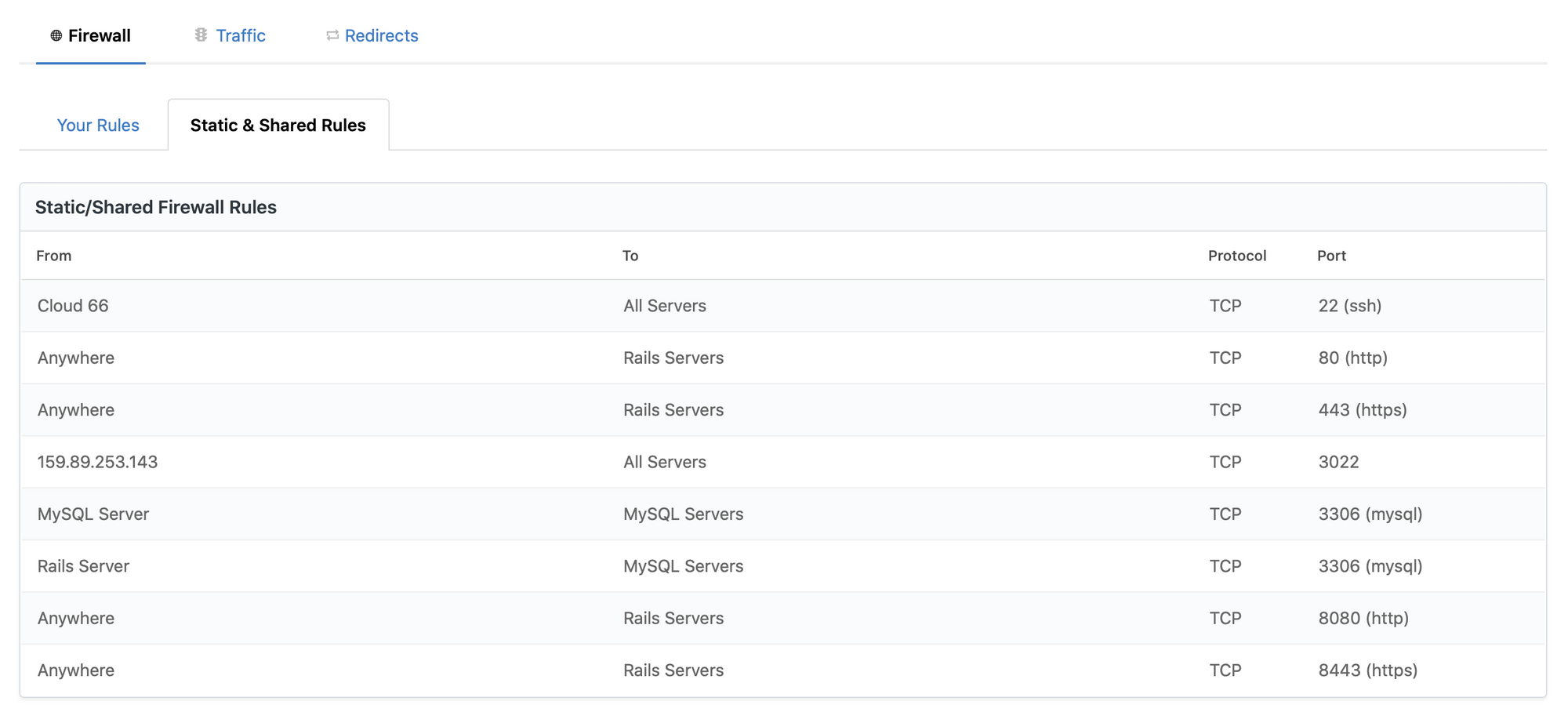
As you can see, instead of IPs we show server roles in rules. This means that when you scale up your database or frontend servers, your firewall gets updated automatically. It also means that when you switch from MySQL to PostgreSQL, the ports also automatically change from 3306 (MySQL port) to 5432 (PostgreSQL port).
More Advanced Scenarios
Cloud 66 firewalls don't stop here. You can configure your network traffic to react to traffic between different stacks automatically. For example, when you share a database between two application stacks, you will need to keep the ports open to the database, not only open to the frontend servers of the same stack, but also to the servers of any other stack that shares this database.
If you need to access a server directly, you can use the Lease feature on the firewall: this allows you to open a port which will be automatically closed after 10 or 20 minutes, which prevents you leaving ports open by mistake.
More info:
- Link to docs: Adding a firewall rule
- Link to docs: Managing advanced firewall rules
- Link to docs: Network security & redirect settings: Firewall
