With the recent OpenSSL security vulnerability just starting to settle down, many of our customers are asking how to rotate their SSL certificates and keys.
Here is a quick review of the process.
Reissue the certificate
Your Certificate Authority (CA) usually gives you a self-service option to reissue certificates. For example RapidSSL allows you to do that by clicking on the "Reissue SSL" link on the right hand side menu.
To reissue a certificate (or issue a brand new one), you need to generate a Certificate Signing Request (CSR) and private key:
$ openssl req -out CSR.csr -new -newkey rsa:2048 -nodes -keyout privateKey.key
This will ask you questions about your company and contact information. The most important part is the common name. This should be exactly the same as the domain you would like to protect. For example to issue a certificate for www.cloud66.com you should enter www.cloud66.com. If you would like to generate a wildcard certificate (which will work with all subdomains of a domain like app.cloud66.com and blog.cloud66.com) you need to enter *.cloud66.com.
Important : Do not enter any passphrases for your key.
Once done, you should have a CSR file and a private key file. Keep your private key, well, private!
Now copy the content of the CSR file to your CA website. On a Max (OSX) you can do this by this command:
$ pbcopy < CSR.csr
Intermediate Certificates and Chains
Some Certificate Authorities are SSL resellers. RapidSSL is one of those companies. This means not all browsers recognise them as a CA. They sell other CA SSLs. In case of RapidSSL for example, it is GeoTrust they resell.
This means you usually pay a lot less for your SSL certificate but you will need to install your intermediate (or chain) certificate on the server as well. You can find the chain certificate for your CA (if applicable) on their site (in RapidSSL case it is here.
Install Your Certificate
To install (or edit) your new key and certificate, click on the "Add SSL Certificate" link under Protips or the padlock icon next to your Web Servers group (if you already have a SSL certificate installed - and then the Edit icon). Here you will be able to enter the new key, certificate and the intermediate certificate (if applicable).
This will automatcally setup SSL with the new keys and certificates on all of your servers.
AWS Load Balancers
If you are using AWS Load Balancers with SSL termination, you can upload the new certificate, key and intermediate certificate by clicking on the Change link under Listeners.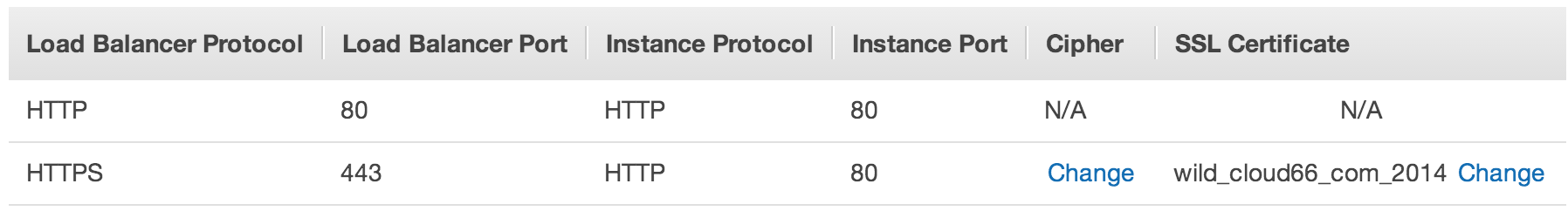
Cloudfront CDN
If you use Cloudfront as your CDN and use SSL SNI with your own certificates to server SSL traffic from your edge servers, you will need to use the AWS command line tool to upload the new certificates to IAM.
Here is the command you will need to run to upload the new key, certificate and the intermediate certificate to use with Cloudfront SSL SNI.
aws iam upload-server-certificate --server-certificate-name my_certificate_name --certificate-body file://my_cert.crt --private-key file://my_key.key --certificate-chain file://intermediate_cert.pem --path /cloudfront/my_cert_name_here/
NOTE : Note the file:// and the trailing / in the command.
Once the files are uploaded, you can choose the right one under Cloudfront settings for your CDN distribution.
